Are You Doing Enough to Prevent Data Breaches?
This post was originally written prior to our January 2017 merger, under our previous firm name, MacPherson Leslie & Tyerman LLP.
Most public and private organizations in Canada share an obligation to protect their clients’ personal information from unauthorized access, use or disclosure. Further, organizations usually have a significant interest in protecting their own business information from such unauthorized access, use or disclosure. One of the key areas of concern for such protection is data breaches. The amount of sensitive information that is vulnerable to data breaches is staggering. It is thus particularly troubling to see that the number of data breaches suffered by public and private organizations are increasing in unprecedented numbers.
This increase was highlighted in the federal Privacy Commissioner’s Annual Report released earlier this month.
The report emphasizes that a record-high number of data breaches were reported in the federal sector, and urges federal departments and agencies to develop and implement more rigorous procedures and safeguards to protect clients’ personal information.
While the report focuses on federal departments and agencies, private entities and provincial public bodies face many of the same challenges in preventing data breaches.
In particular, the rapid pace at which technology evolves means that organizations are faced with an ever increasing number of challenges to data security. To protect against data breaches, it is important to keep abreast of these challenges. One way to do this is to regularly review the common causes of data breaches in order to ensure that your organization’s data security programs are adequate. It is thus useful to review the Report as it provides valuable insight into data breaches and the prevention of such breaches.
What are the common causes of data breaches?
The Report identified 256 data breaches reported by federal departments and agencies in 2014-2015. This number is particularly troubling if one considers that each breach can (and often does) affect thousands of Canadians. The following is a breakdown of the causes of these breaches:
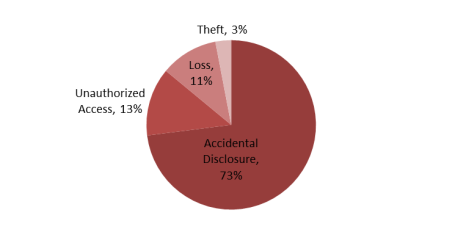
In reviewing this chart, it is notable that nearly three quarters of the breaches were the result of accidental disclosure. Such data breaches could likely have been curtailed with relatively simple steps. In particular, the Report notes that while some of the reported breaches involved network vulnerabilities and technological glitches, a large number of data breaches could have been mitigated with more rigid procedures. As such, the safeguards implemented by organizations can go a long way in preventing and mitigating data breaches.
What can be done to prevent data breaches?
Organizations can implement a number of safeguards to protect themselves and their clients against data breaches. Some of the key steps to prevent data breaches are:
-
Network Penetration Testing and White Knight Hacking:
One key way to ensure that protections are adequate is to test your organization’s networks and systems through the use of network penetration testing or “white knight” hacking. Such testing can help your organization to identify and address vulnerabilities and loopholes in your networks and systems.
-
Due Diligence and Contractual Protections:
Organizations should conduct appropriate due diligence on service providers proposed to provide information and technology services (such as data hosting or system development). Organizations should also ensure that appropriate contractual protections are put in place with all service providers who provide such services.
-
Administrative Safeguards:
- Privacy Compliance Program: Organizations should implement a privacy compliance program that addresses the collection, use and disclosure of personal information. Such a program should include reasonable policies and safeguards (appropriate for the sensitivity of information) to protect information. Once a program is in place, it is critical that an organization conduct appropriate training and enforce the program on a consistent basis.
- Other Policies and Procedures: It is important for organizations to consider and address risks to data security on a case-by-case basis. An organization’s operations will inform the policies and procedures that should be in place. For example, organizations should have appropriate policies in place to address employees’ use of work devices (and personal devices, if permitted), employees’ use of social media, confidentiality of business information, and storage, retention and destruction of information.
-
Physical Safeguards:
Organizations should ensure that appropriate physical security precautions are taken to prevent data breaches. Although the appropriate precautions will depend on your organization, some precautions to consider include keeping information protected from unauthorized access (for example, keep information away from public areas and position or lock devices to protect them from unauthorized access), physically secure information (for example, lock buildings or rooms, restrict access, lock filing cabinets and use alarm systems and security guards) and use secure storage for documents to be retained or destroyed.
-
Technical Safeguards:
Organizations should implement appropriate technical safeguards to address the security of their equipment, software, communications and data. Again, the appropriate technical safeguards will depend on your organization. Some examples include implementing access controls to prevent unauthorized access to devices, unique user names, strong passwords, system audit trails and logs, password-protected screensavers, anti-virus systems and firewalls and security settings and restrictions for mobile devices.
What other steps can your organization take?
In addition to preventing data breaches, organizations should ensure that they are prepared to respond effectively and appropriately to data breaches. Some of the key steps to prepare to respond to (and mitigate the effects of) data breaches are:
-
Breach response programs:
Organizations should adopt and implement programs which guide the organization when a breach occurs. Such programs assist organizations to take appropriate steps in the event of a breach, and usually include the following steps: (1) breach containment and preliminary assessment, (2) evaluation of the risks associated with the breach, (3) notification (where appropriate) and (4) prevention of future breaches.
-
Insurance:
Organizations should consider maintaining insurance that will provide financial protections against a range of liabilities relating to information and technology. Such cyber insurance can provide various protections for your organization against privacy and security liabilities, business interruption and other related risks. Such insurance can also assist in the mitigation of data breaches.
Organizations may wish to discuss their data security programs with legal counsel to ensure that adequate protections are in place and that organizations can mitigate the impact of data breaches to the maximum extent possible. Our team of privacy and cybersecurity lawyers would be happy to assist you.
Note: This article is of a general nature only and is not exhaustive of all possible legal rights or remedies. In addition, laws may change over time and should be interpreted only in the context of particular circumstances such that these materials are not intended to be relied upon or taken as legal advice or opinion. Readers should consult a legal professional for specific advice in any particular situation.